
ERM | RISK TREATMENT
In our latest posts on Enterprise Risk management (ERM), we addressed the three phases of Risk Assessment: Risk Identification and Risk Analysis and Risk Evaluation. In this post, we turn our attention to Risk Treatment.
We manage more than a quarter billion dollars of premiums for a diverse range of clients around the globe.

In our latest posts on Enterprise Risk management (ERM), we addressed the three phases of Risk Assessment: Risk Identification and Risk Analysis and Risk Evaluation. In this post, we turn our attention to Risk Treatment.

Ransomware strikes. Your critical data files have been encrypted and your business grinds to a halt. Do you: a) spend countless hours rebuilding from backups (if you were diligent enough to ensure they’ll work) or b) pay the perpetrator to unlock your files? Now that ransomware is spreading like wildfire through malicious emails, “malvertising” campaigns, and exploit kits, many firms and individuals face this exact scenario.

Globalization and dependence on the internet for data storage over the past decade has exposed companies to a whole new set of risks. As this trend continues, so too does the risk associated with breaches of domestic or international servers. Massive data breaches happen with alarming frequency. In the past few years, there have been several high profile attacks affecting companies like:
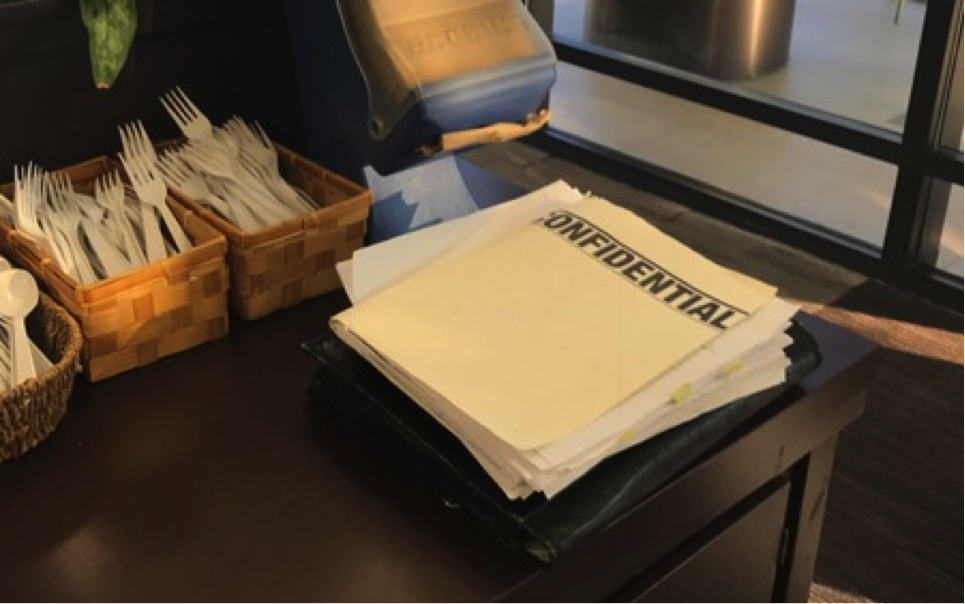
This is an actual picture I took in a café of an unattended pile of documents marked “Confidential.” It blew my mind. If only this employee’s C.E.O. or C.O.O. could see this obvious disregard for the material’s confidentiality. Anyone could have grabbed the documents, peaked at the data, or… snapped a photo.

Cyber risk continues to evolve at a breakneck pace. Insurers are working to keep up by customizing policies and endorsements based on the size and business model of the insured. At last week’s third annual International Cyber Risk Management Conference, Matthew Davies, Assistant Vice President of Chubb Insurance Company of Canada, outlined a few key points on what cyber security practices a small organization to already have in place when looking to procure cyber insurance.
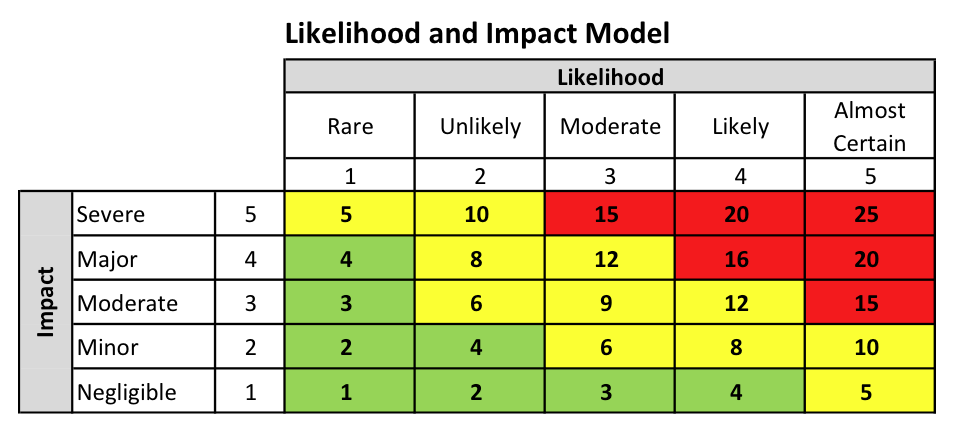
Risk Analysis is the second of three phases that make up a Risk Assessment. What are the other two phases?
In 2015 The Internet Crime Complaint Center received 288,012 complaints of cyber attacks totaling more than $1.07 billion in reported losses. Those numbers are based only on incidents that were reported to the FBI. When we talk about cyber risk, data theft, and the threat of Ransomware, we usually focus on prevention strategies. But being prepared to respond quickly and efficiently when an event does occur is just as important to operations recovery, cost reduction, and reputation management.
Risk Identification is the first of three phases that make up a Risk Assessment.

Most companies today opt to distribute their employees’ W-2 tax forms electronically; either through email or some type of download service. Because these forms contain a good deal of Personally Identifiable Information (“PII”), such as name, address, social security number and salary information – cyber thieves are using several simple, yet, tried-and-true methods to fraudulently obtain them.

In our previous posts in this series, we introduced Enterprise Risk Management (ERM) as a “portfolio view” of risk and discussed various aspects of implementing ERM: roles, culture, a framework and preparing your organization. Now, we’ll begin looking at the “big picture” viewpoint of risk, starting with identifying and prioritizing risks. In the ERM process, management (1) determines acceptable levels of risk, (2) identifies and measures risks throughout the entire organization and aggregates the results, and (3) determines if the aggregated results exceed the acceptable levels. Risk Appetite and Risk Tolerance are the expressions of the “acceptable levels” of risk.