
Newark, NJ City Computers Struck By Ransomware Attack
Multiple sources reported yesterday that hackers encrypted files on computers belonging to the city of Newark and have demanded $30,000 worth of Bitcoin to restore them.
We manage more than a quarter billion dollars of premiums for a diverse range of clients around the globe.

Multiple sources reported yesterday that hackers encrypted files on computers belonging to the city of Newark and have demanded $30,000 worth of Bitcoin to restore them.

Take a casual stroll in Manhattan and you can’t help but notice that construction is booming. Cranes, scaffolding, and sidewalk sheds are everywhere. And this isn’t just a New York City phenomenon. Ground-up construction and renovation projects are picking up all across the country. Low interest rates and favorable building conditions are resulting in a surge in real estate & development projects.

The healthcare sector is without a doubt one of the most targeted industries for cyber hackers. Different industries have different types and degrees of cyber risk exposure. But hackers and malicious campaigns take aim at the healthcare sector in particular due to the private nature and black market value of the data.

Identity theft is the fastest growing crime in the United States. Each year, more than 15 million Americans fall victim. It’s also the number one consumer complaint received by the Federal Trade Commission.

In our latest posts on Enterprise Risk management (ERM), we addressed the three phases of Risk Assessment: Risk Identification and Risk Analysis and Risk Evaluation. In this post, we turn our attention to Risk Treatment.

Ransomware strikes. Your critical data files have been encrypted and your business grinds to a halt. Do you: a) spend countless hours rebuilding from backups (if you were diligent enough to ensure they’ll work) or b) pay the perpetrator to unlock your files? Now that ransomware is spreading like wildfire through malicious emails, “malvertising” campaigns, and exploit kits, many firms and individuals face this exact scenario.

Globalization and dependence on the internet for data storage over the past decade has exposed companies to a whole new set of risks. As this trend continues, so too does the risk associated with breaches of domestic or international servers. Massive data breaches happen with alarming frequency. In the past few years, there have been several high profile attacks affecting companies like:
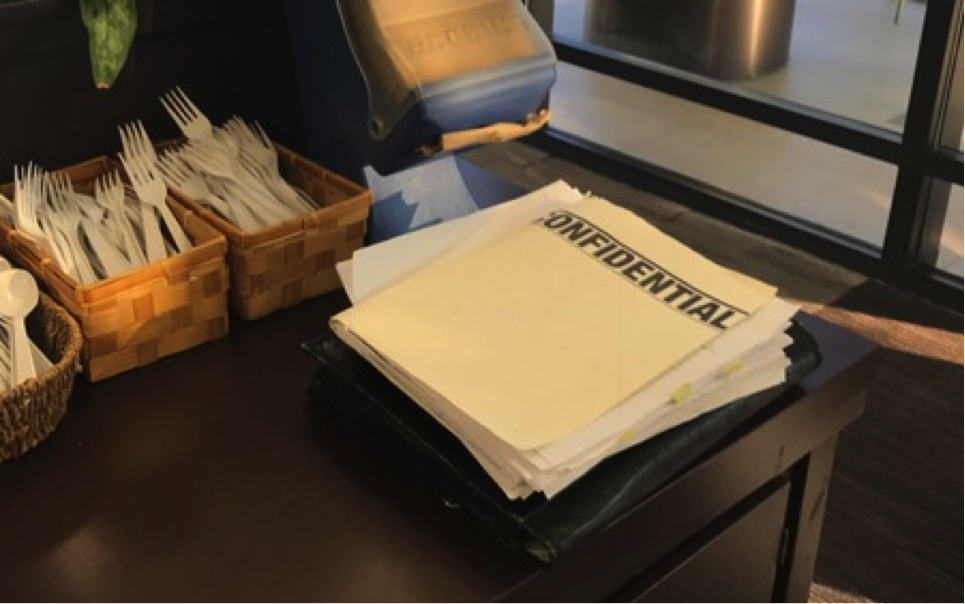
This is an actual picture I took in a café of an unattended pile of documents marked “Confidential.” It blew my mind. If only this employee’s C.E.O. or C.O.O. could see this obvious disregard for the material’s confidentiality. Anyone could have grabbed the documents, peaked at the data, or… snapped a photo.

Errors and even outright fraud in certificates of insurance is a growing problem. We encounter a 70% noncompliance rate on initial documents. The certificate of insurance compliance function protects a company by ensuring that its contractors have appropriate types and amounts of insurance coverage. The burden of this compliance process is often underestimated.

You’ve heard of cyber attacks causing customer data breaches, business interruptions, reputation management issues, and public relations nightmares – but what about physical damage?
Our areas of expertise include:
At The ALS Group, we help clients achieve their strategic goals via expert and insightful identification, quantification, and mitigation of the risks that could impact their business, or present opportunities for it.
More Information: info@thealsgroup.com
Florida
1800 NW Corporate Blvd Ste 202
Boca Raton, FL 33431
Tel: +1-561-437-0024
At The ALS Group, we help clients achieve their strategic goals via expert and insightful identification, quantification, and mitigation of the risks that could impact their business, or present opportunities for it.
More Information : info@thealsgroup.com
New Jersey
175 Main St
Woodbridge, NJ 07095
Tel: +1-732-395-4250
Florida
1800 NW Corporate Blvd Ste 202
Boca Raton, FL 33431
Tel: +1-561-437-0024